Micro CANcrypt: How small can we go?
 Our tutors Christian Keydel and Olaf Pfeiffer published their next security article in the CAN newsletter. This one is about “making security work” for already deployed CAN systems with limited MCU resources available.
Our tutors Christian Keydel and Olaf Pfeiffer published their next security article in the CAN newsletter. This one is about “making security work” for already deployed CAN systems with limited MCU resources available.
Excerpt:
Some things appear to have not changed significantly in the past 20 years of Embedded Systems programming. Back then we would start developing minimal solutions for clients that wanted to add CANopen using “as few resources as possible”. Today, clients want to add CAN security to an already deployed system and again, often with only minimal resources available. Same situation, different technology.
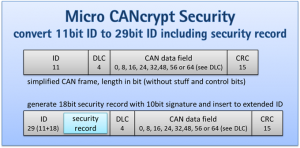
The biggest change compared to unsecured CAN communications is the added security information, and the question is where in the CAN frames we want to put it. In networks that only use 11-bit-identifier CAN frames, like virtually all CANopen systems do, it is convenient if secure frames use a 29-bit CAN identifier instead, as illustrated in figure 1 “Adding security information to a CAN frame”. In the available extra 18-bits long “security record” we can then put a 10-bit signature and some control information. This method greatly simplifies mixing non-secure and secure CAN communications – a secure frame then still uses the same lower 11-bit portion of the 29-bit CAN identifier as the unsecured frame would, and the added security record can be easily recognized. The 18-bit record comprises a 2-bit truncated key refresh counter, a 6-bit truncated timer value and the 10-bit Micro CANcrypt signature. As all devices synchronize their refresh counter and timer locally, the truncated information is enough for receivers to internally maintain the full counter and timer values.
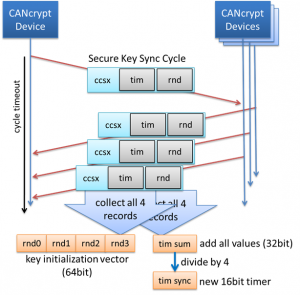
In comparison to CANrypt, Micro CANcrypt uses a simplified key synchronization method. Figure 2 “The Secure Key Sync cycle” illustrates how four event messages use the extended security record to share information. Here the extended security record contains a 16-bit timer and a 16-bit random value. These synchronised messages are used once per second to share / create an initialization vector (IV) for a dynamic, current key from the session key and to synchronize a 16-bit timer value and an 8-bit key refresh counter. A block cipher is used to generate the dynamic key from a shared symmetric permanent key using the IV generated in each cycle.
For more details, read the original article in the CAN Newsletter June 2019
 Deutsch
Deutsch English
English


 Embedded Networking with CAN and CANopen. Your technology guide for implementing CANopen devices.
Embedded Networking with CAN and CANopen. Your technology guide for implementing CANopen devices. Implementing scalable CAN security. Authentication and encryption for higher layer protocols, CAN and CAN-FD
Implementing scalable CAN security. Authentication and encryption for higher layer protocols, CAN and CAN-FD